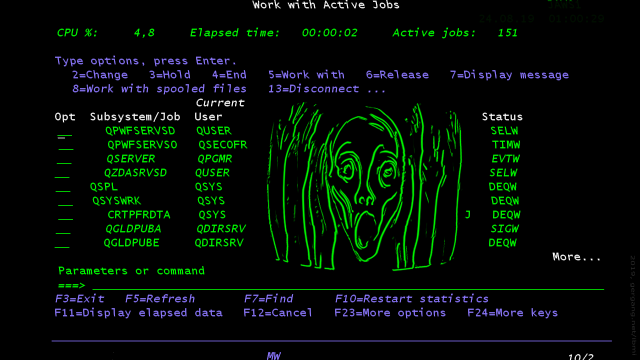
IBM i: A built-in security concept by itself is not enough. Not only does it need to be configured, maintained and enforced, but there are also ways to access data across the network.
Equipped with a simple user profile (or none) exploiting a carelessly configured system security can be relatively easy.
| Topics | |
|---|---|
| 1 - Password Sniffing | Unencrypted Telnet and FTP - the myth is true, passwords are being sent in clear text. |
| 2 - Default Passwords | No outsider knows the profile names anyway... |
| 3 - Third Party Software | How to retrieve "forgotten" passwords in a rather unexpected way. |
| 4 - Spool Control | *SPLCTL gives access to all spool on the system. |
| 5 - Unprotected Profiles | How to properly use unprotected profiles. |
All videos are hosted on Youtube and around 5 min in length.